Alternatives to third-party cookies: what consequences regarding consent?
This article is a courtesy translation of the original in French.
In the event of any inconsistencies between the French version and this English translation, please note that the French version shall prevail.
For several years, some digital stakeholders have been developing alternatives to third-party cookies for advertising targeting. The CNIL, mindful of these innovations, reminds that these technologies must always be compliant with the data protection legal framework, especially, the rules regarding consent and the rights of data subjects.

What is a third-party cookie?
First-party cookies and third-party cookies: what is the difference?
Originally created to enable browsing sessions, for instance by keeping an online shopping basket available to the user, this primary use quickly evolved into advertising tracking purposes, making the cookie a widely used technology in the online advertising ecosystem, particularly through the use of third-party cookies.
When an Internet user visits a website, he/she is in practice visiting a "domain" which usually ends with a .com or .fr extension (e.g. mywebsite.com is a domain). The content of the website visited may be transmitted from the domain that the user visits, or via other domains that the user has not visited, and which belong to third parties. In fact, each cookie is associated with a domain and sent or received each time the browser "calls" that domain. In practice:
- First-party cookies are placed by the website the user is visiting itself, more precisely on the website’s domain. They can be used for the proper functioning of the website or to collect personal data in order to track the user's behaviour for advertising purposes;
- Third party cookies are cookies set by domains other than the one the user is visiting, generally managed by third parties who have been queried by the website visited and not by the Internet user himself/herself: these cookies may also be necessary for the proper functioning of the website, but are mainly used to enable the third party to see which pages have been visited on the site in question by a user and to collect information about him/her, including for advertising purposes.
A tool widely used in the advertising industry
While first-party cookies only allow tracking of the user on the website that place them, third-party cookies allow tracking of the user's behaviour on all the websites that integrate them. This makes them a tool widely used by many online advertising industry’s stakeholders. Thus, for instance, all websites that add a Facebook "like" button or a Youtube video allow, in practice, these actors to receive and place cookies at each visit and thus rebuild a partial browsing history.
Storage of third-party cookies makes it possible to follow the user as he/she navigates from website to website, to collect or deduce from his/her visits information about him/her such as age, place of residence or consumption patterns.
This information can then be used to create a profile of the user, and develop it further, which can sometimes be very detailed and intrusive. This profile is then used to display advertisement that the user is likely to engage with and therefore lead to a purchase.
For many websites, a large part of their revenue comes from the sale of targeted advertising spaces. These transactions involve a multitude of stakeholders and has led to the development of a new part of the advertising industry, generally referred to as "AdTech" (for "advertising technologies"). While it is entirely possible to market advertising without using third-party cookies (for example, an e-commerce site specializing in hiking can display ads from brands in this sector to all its users), the online advertising market is now mainly organized around systems based on third-party cookies and user profiling.
Why are we talking about the end of third-party cookies?
The use of third-party cookies is now being challenged by certain web browsers seeking to limit advertising companies’ tracking possibilities. The forerunner in this area was Apple's Safari browser which, with the launch in 2017 of its ITP program (for "Intelligent Tracking Prevention"), developed browser functions specifically designed to limit certain practices of advertising networks. The proposed system seeks to identify cookies linked to tracking practices and to limit the possibilities offered by APIs to websites, for example in terms of cookies retention duration.
At the end of 2018, it was Firefox's turn to launch a similar initiative called "ETP" (for "Enhanced Tracking Protection"). In practice, with Firefox and Safari, third-party cookies are now limited by default, reducing the tracking capabilities of Internet users based on this technique.
Lastly, in August 2019, Google, whose Chrome browser has a market share of around 70% in 2021, also announced the launch of its project called "Privacy Sandbox”, aiming at limiting the use of cookies for advertising and proposing of technical solutions to retain the advertising features that currently require cookies. This announcement was followed by a commitment from Google to stop Chrome from using third-party cookies by 2023.
However, the end of the use of third-party cookies does not mean the end of tracking Internet users online, particularly for advertising purposes. Indeed, the players in the advertising ecosystem will still be able to use alternative technologies allowing them to track users' browsing and behaviour in order to target them notably for advertising purposes.
An ecosystem in search of alternatives to third-party cookies
In recent years, the CNIL has noted the development of several alternatives to the use of third-party cookies, which can be divided into four categories.
First-party cookies and fingerprinting
Some techniques are used to bypass the restrictions made public by browsers. Different methods are currently used, in a residual way:
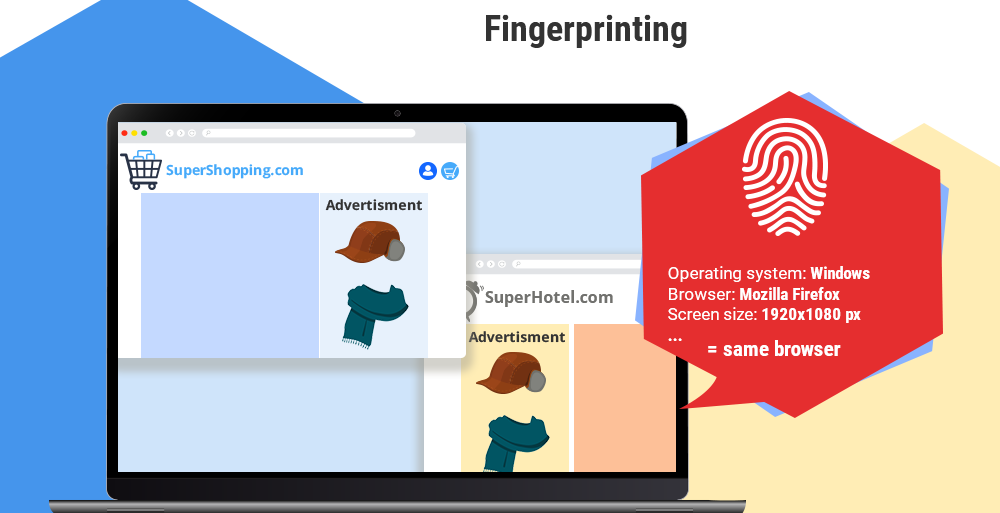
- the fingerprinting aims to uniquely identify a user on a website or mobile application by using the technical characteristics of his/her browser. Indeed, the hardware used for connection provides a certain amount of information to the server, for example the screen size or the operating system. This information, if sufficiently detailed, can be used to set individuals apart (in practice each browser) and to track them in a similar way to cookies.
- The first-party cookies of the website visited by the Internet user can return data via URL calls on the advertiser's domain, or via sub-domain delegation techniques ("CNAME cloaking"). These techniques allow stakeholders that placed third-party cookies to bypass browsers’ blocking by exploiting data from first-party cookies.
Single Sign-On

This system is intended to facilitate the user's connection, but mainly, it allows the group of websites or services to have an overall and consolidated vision of the user's browsing on all the websites, applications or services: the user account becomes a tracker that follows the user during his/her browsing.
Note that: this functionality is not originally designed for advertising targeting. Also, the presence of an SSO is not necessarily linked to advertising purposes (e.g. France Connect).
Unique identifiers
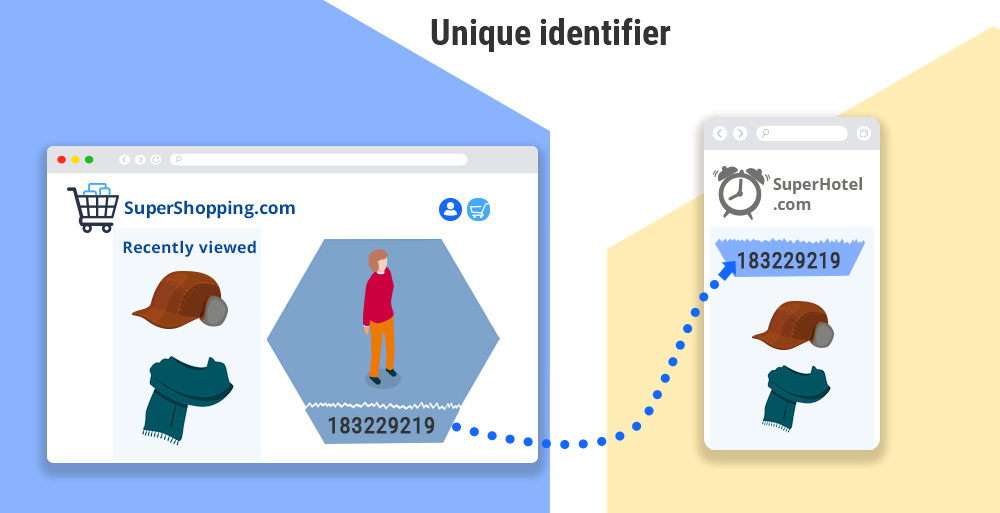
Unique identifiers, developed by analogy with the advertising identifiers assigned to smartphones (e.g. IDFA), make it possible to track a user through the use of a deterministic hashed data, collected during the user's navigation on the website.
This technique can use the email address or a login provided by a user to log into different online services to link these accounts and track the user's use of these services.
This technique is sometimes combined with fingerprinting, one being used to enable the other.
Cohort-based advertising targeting

Some stakeholders, such as Apple or Google, are developing cohort-based targeting systems. In that respect, some of the solutions proposed for instance in the Privacy Sandbox (developed by Google) specifically aim to reproduce the current possibilities of cookies in the context of targeted advertising, while attempting to implement limitations in order to reduce the intrusive nature of these practices.
These limitations consist for example of:
- Cohort-based targeting (FLoC in the case of the Google Privacy Sandbox), which consists in avoiding targeting an individual by focusing on building a group of individuals with similar characteristics (areas of interests, etc.), and which will be identified by a unique and persistent identifier, shared by all users in the same cohort and managed browser level or operating system. In the case of the Privacy Sandbox, the list of domains visited with Chrome is used to calculate the browser's membership cohort, unless the managers of these domains have objected to the targeting;
- Implementing technical solutions that only provide aggregated results to stakeholders, i.e. results that are only presented in aggregate (e.g. only the number of people who have seen an advertising campaign), without access to data on individual views;
- Deporting certain operations (e.g. ad auctions) to the user's terminal in an attempt to limit the ability of stakeholders in the advertising ecosystem to collect information during these operations.
Cohort targeting is in principle less intrusive than third-party cookies: it should allow targeting of a group of users with similar behaviours rather than an individual user.
However, the assessment of the consequences of such a system, and in particular the risks for users' rights and freedoms, depends on a concrete analysis of the way in which targeting without third-party cookies is implemented in order to limit the individual tracking of Internet users (risks of individual re-identification, etc.) and to respect the principle of data minimization.
What are the rules to be respected?
The various techniques above explained raise issues in terms of personal data protection but also in terms of protection of users' terminals and communications. The CNIL reminds the applicable rules.
The CNIL reminds that the development of alternative to third-party cookies must not be made at the expense of the Internet user's right to protection of their personal data and privacy. They must be used in compliance with the principles of the regulations in force, namely the GDPR, but also the privacy and electronic communications directive (known as "ePrivacy") which aim is to specifically protect individuals' communications as transposed into French Act on information technology, data files and civil liberties (Act N°78-17 of 6 January 1978)
This legal framework guarantees everyone protection of their private communications as well as their terminal equipment.
Consent collection: the free choice of the Internet user
The techniques presented above practically all rely on access to the user's terminal equipment (smartphone, laptop or desktop, etc.) to gain access to information already stored in this equipment (advertising identifier, cohort-based identifier, browser setting data) or to record information into it, in the same way as for cookies.
For instance, with regard to FLoC (Google Privacy Sandbox), it is possible for any domain running scripts from a website to access the cohort identifier through the interface offered by the Chrome browser to the website.
In order to protect the integrity of the terminal, actions to access to the user's terminal equipment are particularly regulated by the European texts.
Indeed, the operations, necessary for the constitution of an individual or group profile and the provision of targeted advertising, require the prior consent of the user, whether or not personal data are processed, insofar as they are not directly part of the service directly requested by the user (ePrivacy Directive and Article 82 of the French Act on information technology, data files and civil liberties).
Users must therefore be able to choose freely and in an informed manner:
- to be the object of a tracking not strictly necessary for the provision of the requested service, for example to maximise the relevance of the advertisement presented to their current concerns and, by agreeing to the use of such trackers, to contribute to the remuneration of a site or application; or
- to refuse such tracking.
Please note that: Tracking for advertising purposes, when based on browser or terminal information, must rely on the informed choice of the Internet user, regardless of the technique used. The CNIL’s guidelines and recommendation on cookies and other tracking devices therefore also apply to the use of these techniques.
Other points of attention imposed by the texts
Allow users to keep control over their data
In order to ensure that the use of these technologies respects users’ privacy:
- it is essential to integrate, from the design stage, means enabling users to keep control over their personal data.
It is also necessary to allow and facilitate the exercise of all data subjects’ rights, through user-friendly interfaces, which is a key component of the "privacy by design" approach imposed by the GDPR.
The CNIL prompts actors of the ecosystem to anticipate these constraints, particularly regarding information screens and settings of these new techniques.
Avoiding the processing of sensitive data
Sensitive data are particularly protected under the GDPR: their collection and processing, which are in principle prohibited, therefore call for the utmost alertness. Each actor must ensure that the targeting groups they create do not result in creating discrimination even indirectly.
Remaining responsible for the implementation of these techniques
Finally, the stakeholders (data controllers, processors) must analyze their roles and responsibilities in the implementation of these tracking techniques in order to determine their respective obligations.
CNIL’s special attention
The CNIL remains alert to the development of technologies that enable users to be tracked during their browsing, which must not call into question the rights enjoyed by Internet users.
The CNIL regularly carries out investigations, based on complaints received or on its own initiative, to ensure that technologies proposed to Internet users comply with the legal framework on cookies and other tracking devices, which therefore also apply to all these alternative solutions to third party cookies. In 2021, the CNIL issued several sanctions or formal notices against several digital players (european or not), which did not allow to refuse cookies as easily as to accept them.
The CNIL will closely monitor ongoing developments, both in terms of technical offerings and privacy features in browsers and smartphones, and may publish more detailed analyses.